Identity verification is a critical component of many industries, from finance to healthcare. Traditional methods of identity verification can be slow, error-prone, and costly. AI-powered identity verification offers a transformative solution, enhancing accuracy and...

Spotlight On: The Role of AML in Ending Human Trafficking
Spotlight On: The Role of AML in Ending Human Trafficking
Human trafficking and modern slavery remain two of the most challenging humanitarian issues for international legislators and law enforcement agencies to resolve—due in large part to the the level of difficulty to uncover hidden channels and illegal measures that sustain these trafficking networks. According to the Council on Foreign Relations, there are 49.6 million people around the world living in modern slavery. Of this number, 27.6 million people are subjected to forced labour and 22 million were victims of forced marriages.
With the International Labour Organization estimating that human trafficking generates US$150 billion globally, the cost of failing to prevent such atrocities is clear, and compliance with evolving regulations is undeniably essential.
Preventing human exploitation is critical, and strong AML and KYC protocols are essential in achieving this goal. That’s why incorporating appropriate solutions into your current framework is crucial. Strong compliance software can help eliminate ambiguity and reduce the risk of human error, making it an essential tool in preventing serious crimes and protecting vulnerable individuals. By streamlining your business processes and enhancing compliance protocols, you can achieve better outcomes and safeguard your organization’s reputation.
That’s why we’ve developed an award-winning, truly comprehensive KYC + KYB platform that is designed to eliminate ambiguity and the risk of human error. Our solution produces superior outcomes that not only streamline your business but also help protect vulnerable individuals from serious crimes.
In honour of National Human Trafficking Awareness Day in Canada this February, we’ll take a closer look at some of the global realities of human trafficking, as well as the role of AML when it comes to prevention.
Human Trafficking is a Global Epidemic
The harm caused by any and all forms of human trafficking and exploitation is immense and pervasive in today’s society. As of the end of 2022, 49.6 million victims are still suffering from the danger of human trafficking and modern slavery.
One of the most common misconceptions in the Western hemisphere is that human trafficking is a problem relatively isolated to lower-income countries and geographical regions. In truth, human trafficking affects every country, regardless of its political or socioeconomic standing.
Evolving technology and the ease with which money and other digital assets are exchanged have opened new avenues for traffickers to continuously exploit vulnerable people. At present, the Global Crime Index identifies the highest-risk regions for trafficking as Africa, Asia, Eastern Europe, and parts of Central and South America.
Countries outside these areas are far from exempt; traffickers utilize multiple destinations throughout Canada, the United States, France, Australia, and other “Tier 1” countries (as defined by the Trafficking Victims Protection Act) as transportation hubs to move victims unnoticed.
What is Human Trafficking?
Human trafficking refers to the criminal movement of vulnerable people, regardless of age or status, for the purpose of exploitation. There are several distinct areas of criminality that fall under this terminology:
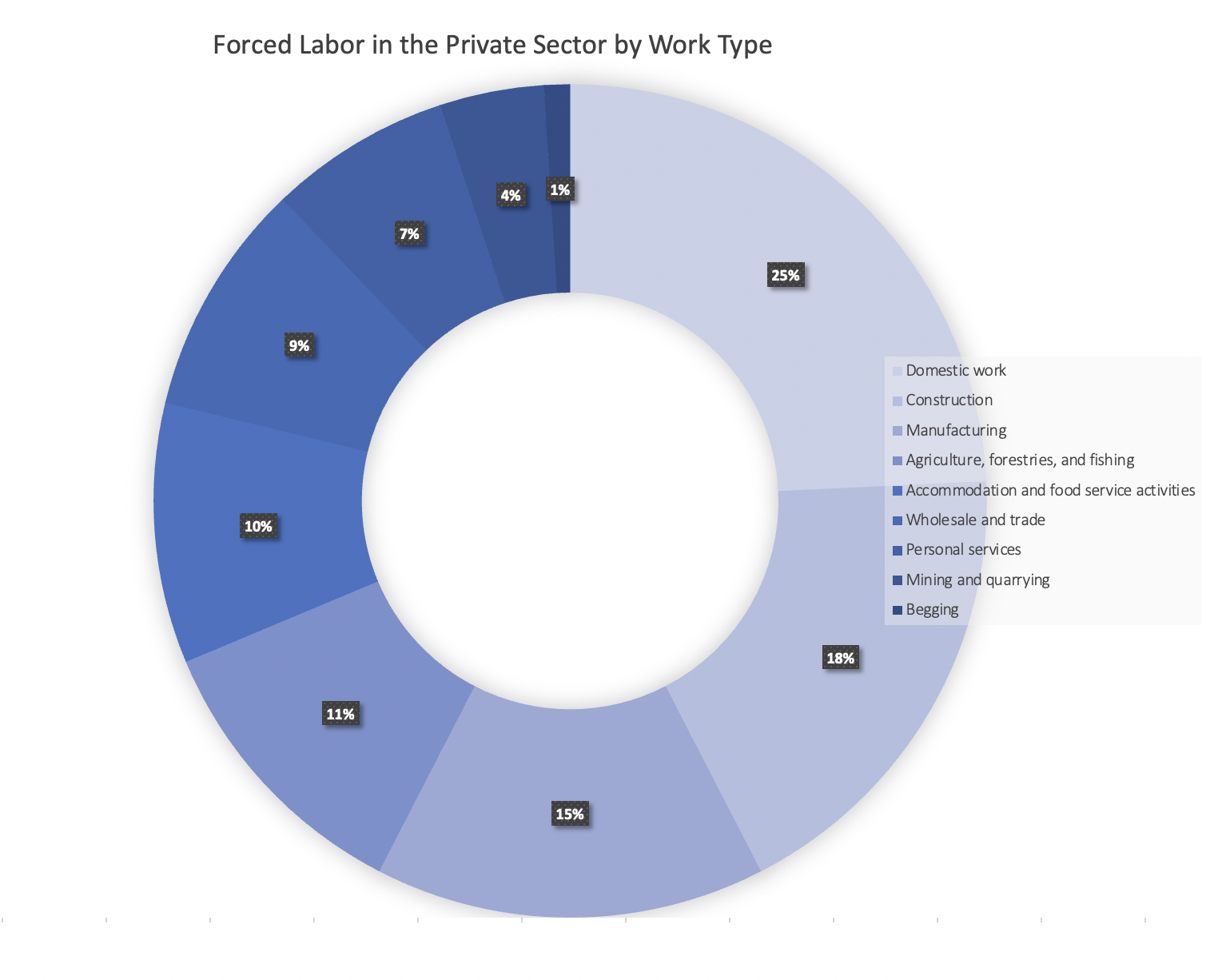
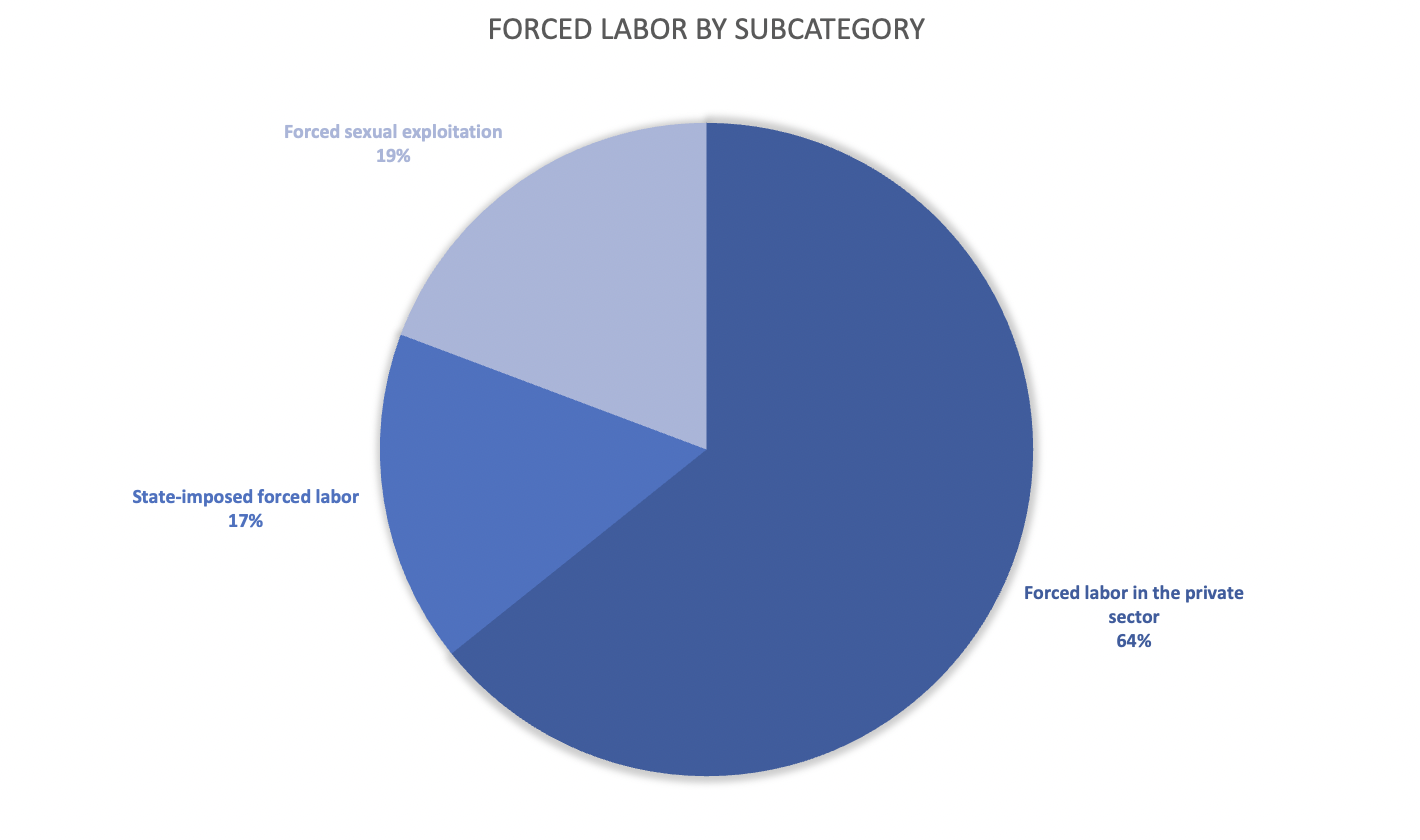
Forced Labour
Forced labour is the exploitation of individuals by forcing them to work for extremely low (often unsustainable living) wages, engage in activities that present significant risks to their health and safety, work under duress or the threat of harm, or labour with no compensation or benefit to the worker whatsoever (therefore, equating to modern slavery). Forced labour victims are often men but frequently include women and children.
As of 2021, the ILO and UNICEF have noted a concerning increase in child labour, rising to an estimated 160 million children, particularly between the ages of 5-11. Children between the ages of 5-17 who are involved in hazardous work (work that is detrimental to their health and/or morals) have also been on the rise, increasing to 79 million victims since 2016. Common avenues for child labour exploitation include agricultural work (predominately farming and livestock herding), factory labour, domestic servitude, militias that use child soldiers, and the commercial sex trade. (Source)
Sexual Exploitation
Sexual slavery makes up a significant portion of human trafficking numbers, with women and children being the predominant victims. Individuals in this category are forced into prostitution rings, sold into international marriages without their consent (e.g. mail-order brides), and forced to engage in sexual acts for money—with the profits primarily or solely benefitting the controlling party.
Medical Exploitation
The Group of International Finance Centre Supervisors (GIFCS) is a long-established group of financial services supervisors that are focused on promoting the adoption of international regulatory standards—especially in the banking, securities, fiduciary, and AML/CFT sectors. The GIFCS represents the interest of its jurisdictional members for various banking matters under the umbrella of funds and securities activities.
Victims of medical exploitation (also referred to as the ‘red market‘) are often subjected to non-consensual experimentation and/or body modification. This includes organ harvesting, forced impregnation, and other forms of human experimentation done with no regard for the lasting harm caused to the involved subjects.
Despite reported decreases in 2020 (largely due to travel complications created by COVID-19), the urgent message of modern slavery remains the same: we must do better when it comes to protecting vulnerable people from human trafficking, and end this threat once and for all.
Why AML and KYC Protocols Matter
Human trafficking is a highly lucrative endeavour for criminals, with many of the activities involved in the sale and exploitation of victims being directly involved in money laundering or surrounding crimes.
Anti-money laundering (AML) and Know Your Customer (KYC) legislation sets valuable safeguards in place that, when widely adopted, can make it significantly more challenging for traffickers to operate covertly.
Proper AML and KYC practices can help identify key signifiers of criminal activities such as:
- the use of “front” or shell companies to launder money
- suspicious capital funnels from multiple (often unknown) sources
- the use of alternative payment methods for nefarious purposes such as cryptocurrencies, prepaid credit cards, electronic transfers, and more
- the concealment of beneficial ownership information
- unusual financial behaviours (e.g. high-frequency transfers, multiple accounts, etc.), and more.
Global regulatory bodies like the Financial Action Task Force (FATF) and regional decision-makers in the EU and North America work continuously to update and refine current regulations (often collaboratively) to identify prevalent risk factors and address the challenges presented by evolving technology and criminal practices.
Reliable software tools to fight financial crimes linked to human trafficking should involve:
- enhanced due diligence,
- transparency into ultimate beneficial ownership structures,
- adverse media screening and known associations with existing criminal networks,
- watchlist monitoring,
- politically-exposed persons (PEP) screening,
- transaction screening,
- and more.
Building a Safer Future with iComplyKYC
Though AML and KYC protocols are, as of yet, unable to fully prevent financial crimes linked to human trafficking, they are some of our most valuable first lines of defence.
At iComply, we are proud to take a firm and unrelenting stance when it comes to preventing the atrocities caused by human trafficking. We believe in the importance of safeguarding both individuals and organizations against criminal accessibility. We are proud to offer a modular suite of KYC and AML products that enable businesses around the globe to comply with local and global legislation designed to stop money laundering and the exploitation of tens of millions of vulnerable people.
iComply acknowledges and stands in support of transparency and education where the dangers of human trafficking are concerned. Our team remains committed to pursuing a safer global financial marketplace—through continued innovation and the development of digital tools you can trust when and where it matters most.
Learn more about the dangers of modern slavery and human trafficking and how the finance sector is working to end it here.
——————————————————————————
Your Partners in Safety and AML Compliance
Learn more about the benefits of iComply’s award-winning suite of AML and KYC software by booking a demo today.
learn more
Is your AML compliance too expensive, time-consuming, or ineffective?
iComply enables financial services providers to reduce costs, risk, and complexity and improve staff capacity, effectiveness, and customer experience.
Request a demo today.
AI-Powered Identity Verification: Leveraging AI for more accurate and efficient identity verification.
Automated KYC Solutions: Tools and Software for Automating KYC Checks
The digital transformation of financial services and other sectors has made Know Your Customer (KYC) processes more critical than ever. Traditional manual KYC methods are often slow, error-prone, and costly. Automated KYC...
Blockchain for KYC: The Benefits and Applications of Blockchain in KYC
Blockchain technology is revolutionizing various sectors by providing secure, transparent, and decentralized solutions. In the realm of Know Your Customer (KYC), blockchain offers significant advantages, enhancing security and...