How to Guide for Identity Data Validation
Identity data validation is a crucial process for financial institutions, fintech companies, and other regulated entities. It involves verifying the accuracy and authenticity of identity information provided by customers during onboarding and ongoing monitoring. Effective identity data validation helps prevent fraud, ensure compliance with regulations, and build trust with customers. This guide will walk you through the steps and best practices for successful identity data validation.
Step-by-Step Guide to Identity Data Validation
- Gather Required Information
Begin by collecting all necessary identity information from the customer. This typically includes: - Full name
- Date of birth
- Address
- Government-issued identification numbers (e.g., Social Security Number, passport number)
- Supporting documents (e.g., utility bills, bank statements)
- Use Reliable Data Sources
Ensure that the data sources you use for validation are reliable and up-to-date. Common sources include: - Government databases
- Credit bureaus
- Public records
- Trusted third-party data providers
- Verify Document Authenticity
Validate the authenticity of the documents provided by the customer. This can be done through: - Document verification tools that check for security features and inconsistencies
- Manual review by trained personnel
- Cross-referencing with government-issued databases
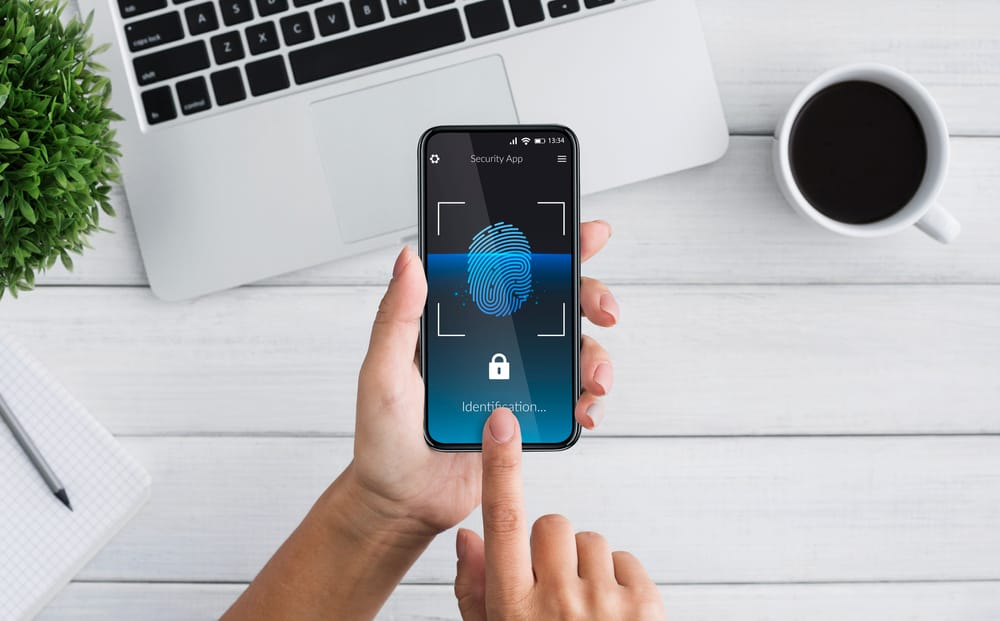
- Biometric Verification
Incorporate biometric verification methods to enhance the accuracy of identity validation. Common techniques include: - Facial recognition technology
- Fingerprint scanning
- Voice recognition
- Cross-check Information
Cross-check the provided information with multiple sources to ensure consistency and accuracy. Discrepancies can indicate potential fraud or errors that need further investigation. - Automate the Process
Use automation tools to streamline the identity data validation process. Automation can help: - Reduce manual errors
- Speed up the validation process
- Ensure consistency in verification
- Ongoing Monitoring
Identity validation is not a one-time process. Implement ongoing monitoring to detect any changes or updates in the customer’s identity information. This can include: - Regularly updating data sources
- Monitoring for any changes in customer behavior
- Revalidating identity information at regular intervals
- Compliance with Regulations
Ensure that your identity data validation processes comply with relevant regulations such as Know Your Customer (KYC), Anti-Money Laundering (AML), and General Data Protection Regulation (GDPR). Staying compliant helps avoid legal penalties and builds customer trust. - Secure Data Handling
Protect the identity information you collect by implementing robust data security measures. This includes: - Encryption of data at rest and in transit
- Access controls to limit who can view and edit data
- Regular security audits to identify and mitigate vulnerabilities
Best Practices for Identity Data Validation
- Use a Multi-Layered Approach: Combine various verification methods (e.g., document verification, biometric checks, database cross-referencing) to enhance accuracy.
- Keep Systems Updated: Regularly update your systems and data sources to ensure they reflect the latest information and technologies.
- Train Personnel: Provide ongoing training for staff involved in identity validation to keep them informed about the latest tools and techniques.
- Engage Third-party Providers: Utilize third-party providers for specialized validation services to complement your in-house capabilities.
Identity data validation is a fundamental aspect of ensuring security, compliance, and trust in financial services. By following these steps and best practices, institutions can effectively validate customer identities, prevent fraud, and meet regulatory requirements. Implementing a robust identity validation process not only protects your organization but also enhances customer confidence in your services.
For a comprehensive and integrated solution to manage your identity data validation, consider iComply. Our platform offers advanced features and tools to help you validate identities accurately and efficiently. Contact us today to learn more about how iComply can support your compliance needs.